Using Yasuo to Scan for Vulnerable Web Apps
Streamline your Penetration Testing with Yasuo
0xsauby saw that he was repeating many common steps for detecting vulnerable web applications during penetration tests and decided to create a tool to automate that process. He later enlisted the help of logicalsec to enhance it.
Yasuo also searches for far more vulnerabilities than would be typical in a manual search for the low hanging fruit like default Apache Tomcat and Jenkins installs.
I had the privilege of working with them at Security Compass.
For a better overview of Yasuo, here's a SlideShare presentation about Yasuo that was presented at Derbycon 4.0 and several other conferences.
Yasuo is available on GitHub. It is open source.
Use case
Many, many tools exist for web app vulnerability scanning. When would Yasuo be a fit?
Let's say you have a penetration test for a customer that has a lot of IP's in scope, but does not want or allow you to use a conventional vulnerability scanner like Nessus Pro. You suspect there may be vulnerable web services out there. Yasuo may be a fit.
It lets you quickly scan a large number of web servers for vulnerabilities that are very likely to lead to quick system access.
Installation
I installed Yasuo on a locally running Kali Linux VM.
Prepare the system by installing prerequisites:
gem install ruby-nmap net-http-persistent mechanize text-table sqlite3
It errored out on the sqlite3 installation, so I had to provide access to sqlite3 headers they try again.
apt-get install libsqlite3-dev
gem install sqlite3
If all goes well, cd to \opt\ or your directory of choice, then create a local copy of the git repo.
If you get errors, try, try, try again until it they're fixed.
cd \opt
git clone https://github.com/0xsauby/yasuo.git
cd yasuo
The options for running Yasuo are presented on its GitHub page.
Unable to guess what the option yasuo -h might do, I had to run it to see that it generates the helpful help output.

Who would have known?
(For those who don't know me, or weren't sure, that was a joke. -h is very often provides help output in the Linux world)
Using Yasuo
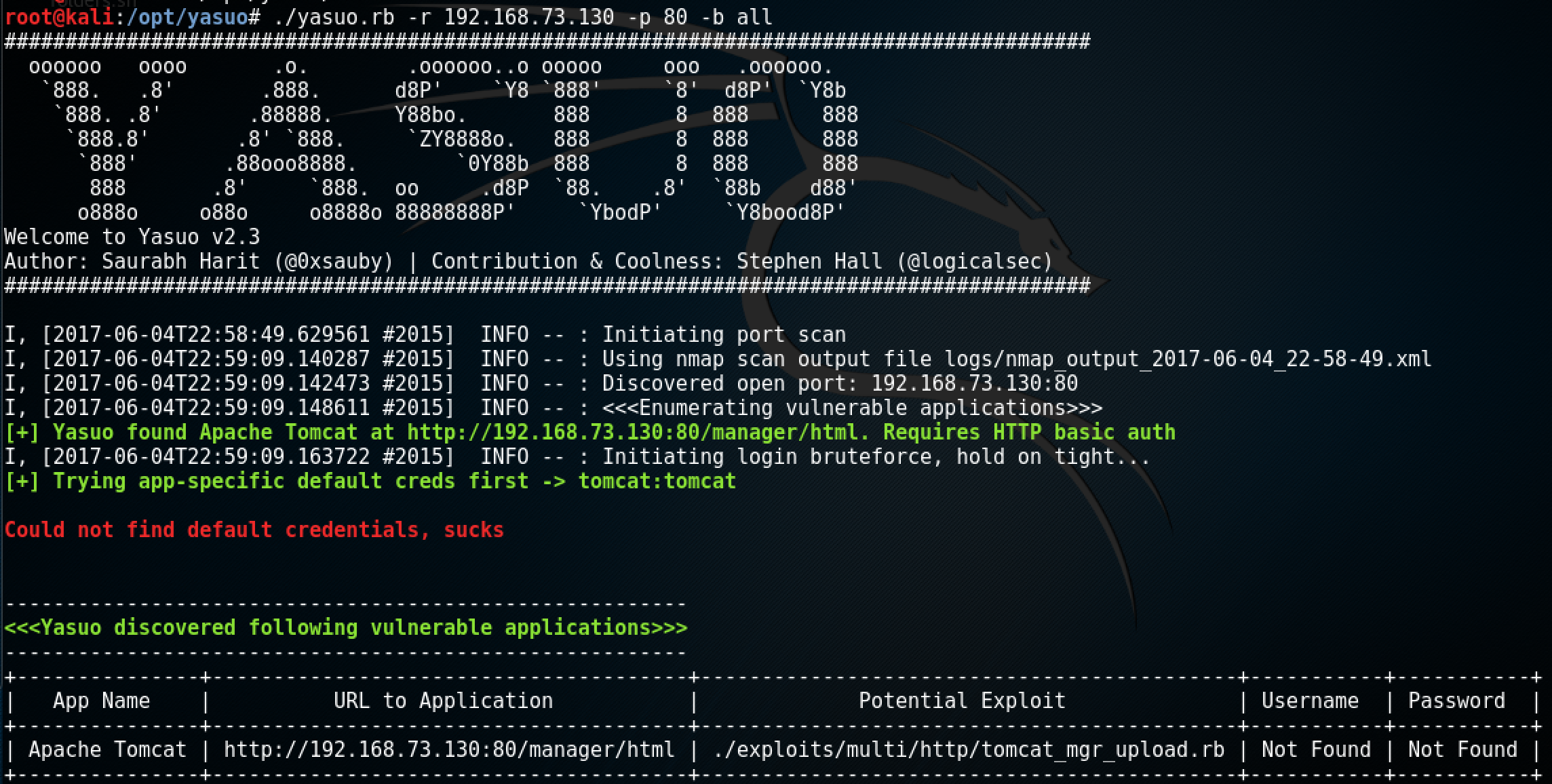
I ran Yasuo against a vulnerable axis2 and Tomcat iso. I downloaded from vulnhub and created a VMware VM from it. It found the Tomcat install but the login wasn't default.

[more to come... finding other vulnerable servers to test]


