Harden Your Docker Deployment With Free Tools
With Docker vulnerabilities in the news of late, it makes sense to have a look at hardening your deployments, especially any that are exposed to the Internet.
Things you can do to protect yourself, as with any system exposed to the Internet include:
- Patching your applications and keeping them up to date
- Patching and hardening the underlying server operating systems
- Patching and hardening your Docker installation
Of course, you should roll out secure operating systems and applications always, and patch frequently regardless of the current threat so you're not scurrying around in a panic whenever a critical vulnerability is released.
A free tool you can use to help secure your base operating system is the Center for Internet Security's CIS Benchmark for your operating system. I have an article with an overview on using CIS Benchmarks to harden Ubuntu 18.04 Server you can check out. As mentioned in the article, the open source tool, Lynis, can help you evaluate your system's security. Use Lynis on your Linux, BSD, and Mac OS X systems.
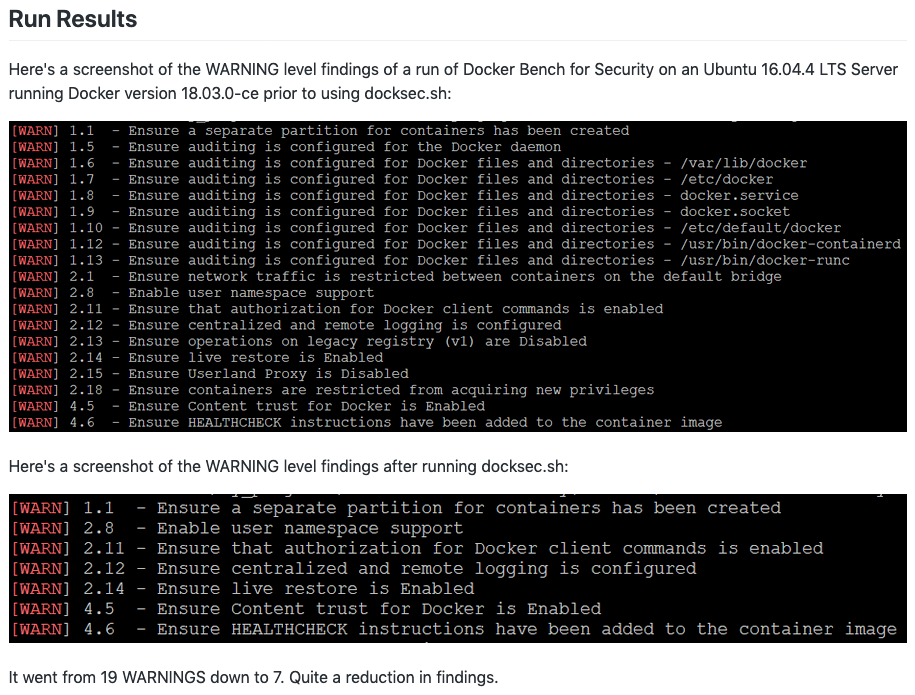
For hardening your Docker installation, there is a CIS Benchmark available, and a free tool called Docker Bench for Security that will do a scan similar to that done by Lynis for the operating system.
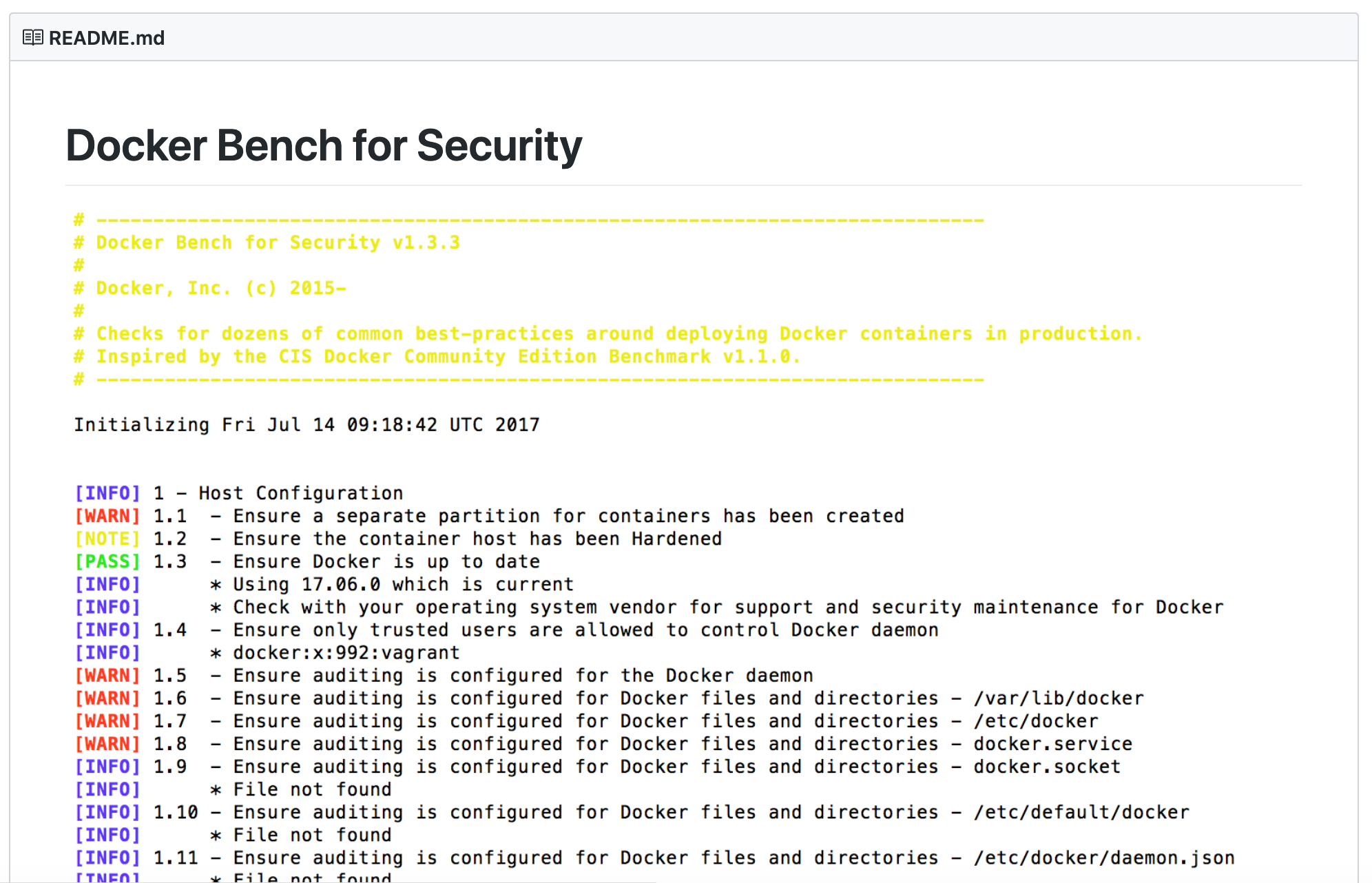
You're free to run Docker Bench for Security on your Docker system, look up the relevant item in the CIS Benchmark for Docker, and manually make the edits to harden your system, or you could run my docksec.sh script and handle many of the steps for you! It was started at a Hackathon at work and has had some refinements since its initial release. Work did authorize me to release it as an open source project for all to use.
Give these things a try to secure your systems.
To recap, as always, you should:
- Secure your applications
- Secure your base operating system
- Secure your Docker deployment
Don't get hacked. Enjoy!