Deploying a Modern Honeynet (MHN) Server
Watch real-time attacks with a Modern Honeynet (MHN) Server and MHN sensors
Honeypots are servers specifically designed to catch malicious traffic and users in action. Honeynets are networks for catching them.
The Modern Honeynet project's goal is to make honeynets accessible to anyone willing to give them a try.
Once you deploy a MHN server with the steps below, you can then deploy sensors and have them report their hits to the server.
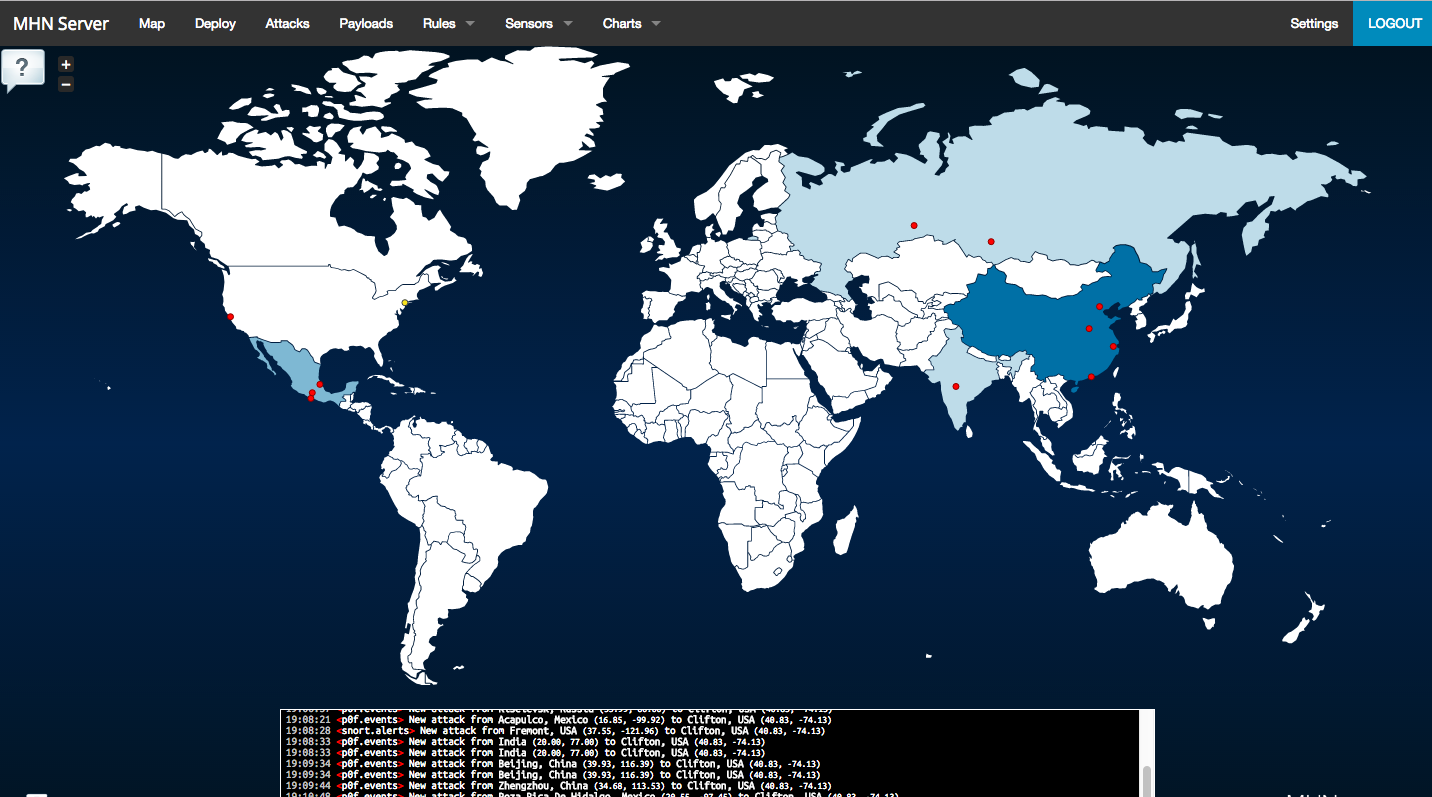
MHN even provides you with a cool map of the hits once you have a sensor deployed:
Create a base build using the steps provided, but make sure you choose an Ubuntu 14.04.x server build. MHN's git page says to use 12.04, but I used 14.04.5 and it works.
Enable ufw, but allow ports 22, 80, 443, 3000, and 10000.
ufw allow ssh
ufw allow 80
ufw allow 443
ufw allow 3000
ufw allow 10000
ufw enable
ufw status
Output should look like this:
root@ubuntu-Test8888:/opt/mhn# ufw status
Status: active
To Action From
-- ------ ----
22 ALLOW Anywhere
80 ALLOW Anywhere
443 ALLOW Anywhere
3000 ALLOW Anywhere
10000 ALLOW Anywhere
22 (v6) ALLOW Anywhere (v6)
80 (v6) ALLOW Anywhere (v6)
443 (v6) ALLOW Anywhere (v6)
3000 (v6) ALLOW Anywhere (v6)
10000 (v6) ALLOW Anywhere (v6)
If you didn't type the IP address of your server during setup for the Honeymap url question, your map won't work until you do the following:
Edit the /opt/mhn/server/config.py file to update the HONEYMAP_URL server name.
cp /opt/mhn/server/config.py /opt/mhn/server/config.py.00
vim /opt/mhn/serve/config.py
Find the line HONEYMAP_URL
HONEYMAP_URL = ':3000'
Edit to read as follows
HONEYMAP_URL = 'http://<your server IP>:3000'
Replacing
You can obtain this by typing
ifconfig | grep inet
and looking for the line with a public IP address.
After saving the edited file, restart the celery service.
sudo supervisorctl restart mhn-uwsgi
Once your server is deployed, log in to it by browsing to the IP address and entering the email address and password you entered during setup.
Check the status of your server
To see how the MHN related services are running, type supervisorctl status.
If you see mhn-celery-worker FATAL Exited too quickly (process log may have details), you may have to change ownership of the mhn.log file (I had to do this sometimes). chown www-data /var/log/mhn/mhn.log. The type supervisorctl start mhn-celery-worker. It should now start normally.
Remember, spinning up DigitalOcean servers costs you money. There's also some risk in taunting the bad guys. I recommend spinning up a sensor and collecting data for a few hours to a few days, then shutting it down and destroying it. You can quickly spin up a new one if you saved an image of your secure base build.
You can deploy sensors quickly and easily which is covered in my next post.
