Deploying Modern Honeynet (MHN) Sensors
My last post was about deploying a MHN Server. This one is about deploying MHN Sensors which feed their data on real-time attacks to the server.
To deploy a sensor, spin up an Ubuntu 16.04 reasonably secure Droplet.
This should have been done during your server build, but make sure everything's up to date.
apt-get update && apt-get upgrade -y && apt-get dist-upgrade -y
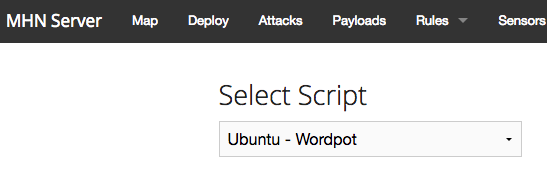
Browse to the MHN Server and click on the Deploy link in the top menu.
Choose a type of Honeypot you'd like to deploy (in this case I chose Ubuntu Wordpot).

MHN has built in support for the following sensors:

- Ubuntu - Wordpot - A WordPress emulator.
- Ubuntu - p0f - Passive OS Fingerprinting.
- Ubuntu - Shockpot - Detects Shell Shock exploit attempts.
- Ubuntu - cowrie - SSH and Telnet honeypot.
- Ubuntu - Suricata - Intrusion Detection System.
- Raspberry Pi - Dionaea - Malware capturing honeypot.
- Redhat/Centos - Kippo - SSH honeypot.
- Ubuntu - Kippo as vulnerable Juniper Netscreen
- Ubuntu - Conpot - Industrial Control Systems honeypot.
- Ubuntu/Raspberry Pi - Kippo - SSH honeypot.
- Ubuntu - ElasticHoney - Elasticsearch honeypot.
- Ubuntu - Amun - Python honeypot.
- Ubuntu - Dionaea with HTTP - Malware capturing honeypot.
- Ubuntu - Snort - Intrusion Detection System.
- Ubuntu - Dionaea - Malware capturing honeypot.
- Ubuntu - Shockpot Sinkhole - Shellshock detection and sinkholing.
Copy the script from the server into a root or sudo command prompt on the new Ubuntu droplet you intend to use as your sensor.
cd /opt/
wget "http://<your server's ip>/api/script/?text=true&script_id=17" -O deploy.sh && sudo bash deploy.sh http://<your server's IP>. <generated password>
Watch as the script runs to make sure the sensor is built properly.
Once it's deployed, you should see it in your web browser on the server. Click on View Sensors under the Sensors menu item.

That sensor was destroyed before I posted this, so the IP Address is visible.
Also, remember that you want people to hit open ports on your sensors. Depending on what kind of sensor you spin up, you'll want to permit the applicable connections through via open ports in your firewall.
For wordpot for example, you'll want to permit ports 80 and 443.
ufw allow 80
ufw allow 443
For kippo, you'll want to allow SSH.
ufw allow 22
You get the idea.
To see what ports the server is trying to listen on, use netstat.
netstat -tanup
Look at the output and see what ports it's listening on and allow those through the firewall.
Anomoli has put out some recommended use cases with some combinations of sensors you may be interested in.
MHN Security
Provided you configure your sensor using a secure base image, you should not have to do much extra to secure it. All honeypots are Low to Medium interaction honeypots.
MHN's security recommendations are to leave firewalls off on your sensors. I enable them for many sensor types. If I have a sensor that is only supposed to be analyzing traffic on port 22 (SSH), I block access to other ports.
If you want to get adventurous, and the server is actually listening for other types of activity, you can certainly disable ufw or open other ports.